Secure IT Infrastructure 2029690519 Online
A secure IT infrastructure is essential for modern organizations, serving as a foundation for data protection and operational integrity. Key components include encryption, access controls, and network segmentation, which collectively mitigate vulnerabilities. Regular security audits further enhance resilience against emerging threats. However, as cyber risks evolve, understanding the latest technologies and best practices becomes imperative. This leads to crucial questions about future preparedness and the ongoing commitment to security excellence.
Understanding Secure IT Infrastructure: Key Components and Benefits
A secure IT infrastructure serves as the backbone of an organization’s digital environment, encompassing various components that work synergistically to protect data and maintain system integrity.
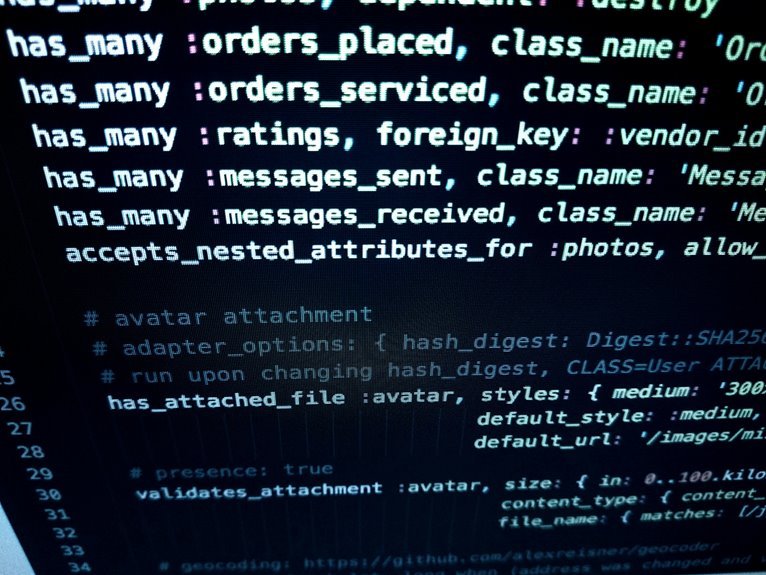
Key elements include data encryption, which safeguards sensitive information from unauthorized access, and network segmentation, which isolates critical systems to minimize vulnerabilities.
Together, these components enhance security posture, enabling organizations to safeguard their assets while promoting operational freedom.
Essential Technologies for Strengthening IT Security
To bolster IT security, organizations must implement a variety of technologies designed to address specific vulnerabilities and enhance overall defense mechanisms.
Key components include robust encryption methods to protect sensitive data and stringent access controls to ensure that only authorized personnel can access critical systems.
These technologies not only mitigate risks but also empower organizations to maintain control over their digital assets securely.
Best Practices for Maintaining a Safe IT Environment
While implementing advanced technologies is crucial for IT security, maintaining a safe IT environment also hinges on adherence to established best practices.
Regular security audits are essential for identifying vulnerabilities and ensuring compliance.
Additionally, comprehensive user training empowers employees to recognize potential threats, fostering a culture of security awareness.
These strategies collectively enhance resilience against cyber threats, supporting organizational freedom and integrity in operations.
Preparing for Future Threats: Trends in IT Security?
As organizations increasingly rely on digital infrastructures, the landscape of IT security is evolving, necessitating a proactive approach to identifying and mitigating emerging threats.
Trends indicate a shift towards security automation, enabling real-time threat detection and response. By leveraging advanced technologies, organizations can enhance their resilience against sophisticated attacks, ensuring a more secure and adaptive IT environment that aligns with the demand for freedom and innovation.
Conclusion
In conclusion, establishing a secure IT infrastructure is paramount for organizations navigating today’s digital landscape. By integrating essential technologies and adhering to best practices, businesses can proactively defend against evolving threats, much like knights donning armor in medieval battles. Fostering a culture of security awareness among employees further enhances resilience, ensuring compliance with regulatory standards. As threats continue to advance, organizations must remain vigilant, adapting their strategies to safeguard sensitive data and maintain trust with stakeholders.